Mining Algorithms For Processors, Graphics Cards And Asics
Crypto mining algorithms are a specific structure (encryption mechanism) that is unique to different digital currencies. The performance depends on the power of the hardware and ability to be applied for mining a particular coin. In the process, miners use hardware with a high hash rate required to find the single correct number and form a block of the cryptocurrency network. The result of the work is a bonus for the mined block.
Today, there are around thirty mining algorithms, but the popular ones include no more than ten, which are the basis of the popular and sought-after digital money in the cryptocurrency community. The rest are used for “young” and unclaimed coins, so there is no point in considering them.
Table of Contents
Algorithms for mining on CPUs
Various protocols are suitable for CPU mining, including SHA-256, Scrypt and others. Popular digital currencies such as Bitcoin, Litecoin and others with high mining complexity work on them. The low processing power of CPUs does not allow them to compete with graphics cards and ASICs, so users are forced to look for other options. Two algorithms are suitable for mining on a CPU.
Yescrypt
Only two cryptocurrencies work GlobalBoost and Unitus. The above-mentioned coins have a low price and mining complexity, so mining them with a processor is not a problem. The main thing is to be careful in setting up your equipment and choosing a pool to mine the coins.
CryptoNight
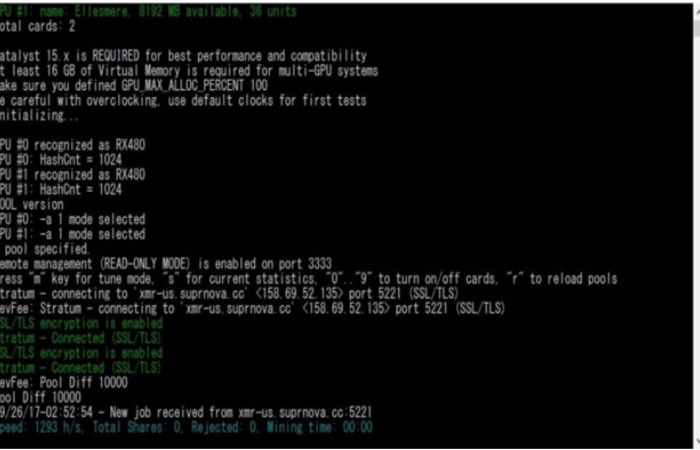
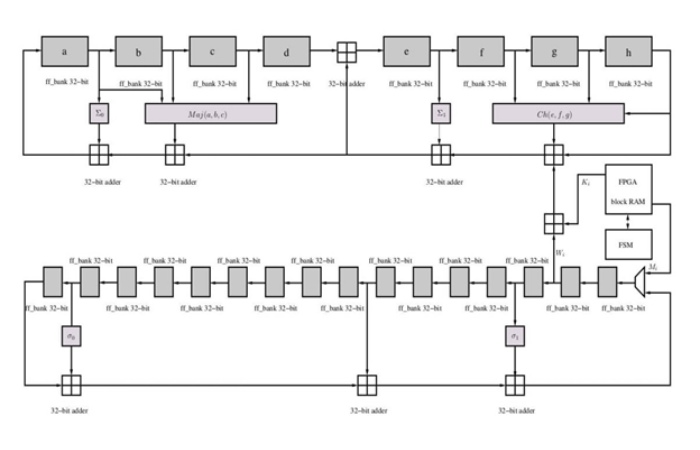
An advanced algorithm based on the PoW consensus mechanism. Originally created for CryptoNight. Then, a Bytecoin coin was created. Subsequently, Monero, Dashcoin and other cryptocurrencies were added to this list. During the creation process, the developers focused on protecting CryptoNight from centralization. The plan was to make digital money mining accessible to participants with ordinary PCs and to protect against ASICs.
Unlike Scrypt, in CryptoNight the new chain elements depend on other nodes (obtained earlier). Two megabytes of RAM (the minimum cache size for processors) are required for control. This feature eliminates the use of ASICs for mining cryptocurrencies, including Monero.
Additional features of CryptoNight are higher requirements for confidentiality (protection of user information) and high requests for RAM. To maintain anonymity, a special scheme is used to ensure that information about the sender is preserved.
CryptoNight operates on the principle of a ring signature. If someone has signed a transaction, it is accepted by the system. Unlike other algorithms, cryptocurrencies based on CryptoNight are well mined on CPUs using XMR-Stak (for Monero), Claymore’s CryptoNote and other programs. AMD models with higher performance are recommended for mining.
It is important to consider the Lite, v1 and Heavy branches of the CryptoNight algorithm. The first is suitable for mobile phones, the second is designed to combat ASIC miners and the third is considered the exact opposite of the Lite version.
These are the main algorithms for mining on CPUs. For the other protocols, the use of CPUs is generally unprofitable (even in the case of modern CPUs).
Algorithms for ASICs
The first ASIC miners, created in 2014, immediately gained the affection of miners. Their advantages were their small size, minimal power consumption and high performance, which is important for mining. Initially, ASICs were produced under SHA-256, but today the choice of devices is wider. Six algorithms are used for mining on ASIC miners.
SHA-256
Suitable for Bitcoin, Namecoin, Terracoin, Bitcoin Cash and several other digital coins. The protocol abbreviation is “secure hashing algorithm”. The release of the second version of the SHA dates back to 2001, and the main use is as a security standard for the United States NSA.
The “Zero” version of SHA was released long before that (in 1993), and SHA-1 appeared two years later. The number 256 represents the size of the messages (256 bits). The encrypted information is called a hash, and the time to process the block is about ten minutes. A new block appears after a single correct value is matched.
SHA-256 is suitable for CPU mining if the complexity of the crypto-network is low. In the case of BTC or its fork (Bitcoin Cash), the mining efficiency is zero. ASIC miners are used to mine new coins (including Bitcoin).
Popular models include the BitmainAntMiner T9+, BitmainAntMiner S9, Canaan AvalonMiner 821, EbangEbit E 10.1 Miner 18T. Performance of the mentioned equipment ranging from 10 to 18 TX/s, depending on the model.
Scrypt
The first cryptocurrency after Bitcoin was Litecoin, which is based on the Scrypt algorithm. Today, there are different cryptocurrencies using this protocol: Novacoin, Verge, Dogecoin, Florincoin and others. The protocol features a large number of layers, triggered by the SHA-256 process.
Finding the hash is made more difficult by the appearance of noise from random digits. A password is used to create the key, so the hacking process is difficult. It is not possible to attack a system by guessing a single correct value.
Using Scrypt requires hardware with more RAM, that is why ASIC miners on Scrypt did not appear immediately. The advantages of the protocol are lower power consumption and the ability to mine on simpler equipment such as processors or graphics cards. Due to the high complexity of mining Litecoin, it is unprofitable to mine this cryptocurrency using CPUs or GPUs.
What makes Scrypt special is its ability to substitute the hash value with a smaller parameter. This factor ensures a better speed of operation. It takes about 30 seconds to form a new chain element. Popular programs for mining on the algorithm: CGMiner, SGMiner and others.
Along with some ASIC miners comes software, making the task easier for the miner. Popular ASICs running on Scrypt are BitmainAntminer L3+, Innosilicon A6 LTC Master, Innosilicon A4+ LTC Master, BW L-21. Hash rates of the above devices range from 504 to 1230 MX/s.
X11
An algorithm created in 2014. It powers Dash, Cannabis Coin and Startcoin. The protocol was created for the cryptocurrency DarkCoin, later renamed Dash. The creator’s goal was to make a mining algorithm that was resistant to the processing power of ASIC miners. To achieve this, 11 different hash functions were combined in X11. The developer is Evan Duffield.
The creator’s aspirations were not successful – soon after ASICs, Dash mining devices appeared on Scrypt. The most popular models are Innosilicon A5 DashMaster, Pinidea ASIC X11 Miner DR-100, BitmainAntMiner D3, iBeLink DM22G X11/Dash Miner. The throughput of the mentioned machines is from 19 to 32,5 GH/s.
Advantages of X11 are safety, low entry threshold and possibility for mining on weak hardware (for “young” coins). The program is CCMiner. Today, the trend of X11 is continuing. This led to the appearance of protocols from X12 and higher (up to X17). The difference is the greater number of features applied.
Ethash
A unique algorithm created specifically for Ethereum mining. Development began in 2013, but the algorithm has been functioning since 2015 (it appeared along with the cryptocurrency). In 2016, a hardfork occurred. As a result, Ethereum Classic was spun off (the digital coin is mined on Ethash). The creator is VitalikButerin.
The Ethash algorithm works as follows. The task of the mining hardware is to capture elements of the data set and then merge them. The information is updated at intervals of once every 30,000 blocks. During the development of the algorithm, emphasis was placed on resilience to ASICs.
The first ASIC device on Ethash appeared in 2018. The only representative is BitmainAntminer E3. The hash rate is 190 MX/s. In addition to ASICs, powerful NVIDIA graphics cards, such as the 1080 Ti, can be used to mine Ethereum.
Equihash
The Zcash mining algorithm, which has gained popularity due to the aforementioned cryptocurrency. In addition to Zcash, Horizen, Bitcoin Gold, ZenCash and other less popular coins run on the protocol. The Equihash peculiarity is the increased RAM requirements (from 2 gigabytes and above). The developers are Biryukov A. and Khovratovich D.
The essence of the protocol is to increase the probability of obtaining the required hash with an increase in the number of participants. The probability of finding it is two raised to the power of “N” and divided by two. In 2017, the first ASIC for mining coins on Equihash, Antminer Z9 mini, appeared, and after a further time the AntMiner Z9. The performance is from 10 Ksol/s.
Blake-256 (r14 or r8)
The hybrid systems that strike a balance between PoW and PoS. Both algorithms can be used for mining on graphics cards or ASIC miners. The developers are considered to be four people – Henzen L., Aumasson F., Phan R., Meier W.
Advantages: simplicity, clear interface, reduced hardware requirements, fast data processing and customizability. Blake-256 is tamper-proof, resistant to increasing hash size and protected against attacks from the outside channel.
The following cryptocurrencies work on the algorithm: Blakecoin, Decred, Dirac and others. The ASIC for mining is AntMiner DR3. The performance is 7.8 TX/s.
For other algorithms, ASIC miners are not made yet.
GPU mining algorithms
With the advent of Bitcoin in 2009, miners started mining with CPUs, but as the complexity increased, they switched to using graphics cards (GPUs). The equipment has better performance and the ability to perform a greater number of hash lookups. NVIDIA 1080 Ti (the best representative of GPU today) gives good mining results.
Equihash, Ethash, SHA-256, Scrypt and other protocols are suitable for mining on graphics cards. Much depends on the complexity of the cryptocurrency network and the popularity of the cryptocurrency being mined.
Additionally, the following algorithms are worth highlighting:
1.Groestl – algorithm used for mining the cryptocurrency of the same name as well as Diamond. It was specifically developed for the SHA-3 function competition. It was developed by a team from the Danish Technical University. Features: reliability and the ability to use processors for cryptocurrency mining.
2. Lara2z is a mining algorithm designed to combat miners and botnets. Today it is used by Zcoin, Inditex and Taler cryptocurrencies. Lara2z is based on a combination of Blake-256 and Lyra Advantages: resistance to attacks, ability to make corrections to basic settings, and high processing speed. It is currently the coolest mining algorithm due to the minimal electricity used. Lara2z is resistant to ASIC miners; miners use graphics cards and SGMiner, Nemos Miner and other programs.
Other Algorithms
When selecting algorithms for mining, it is important to consider other popular protocols:
- NeoScrypt is an improved version of Scrypt. It was created to reduce the impact of ASIC miners and allow mining with simpler devices. The peculiarity of NeoScrypt is the low complexity of the crypto network and mining of 60 to 90 coins per block. The protocol has a high transaction speed thanks to fast user authentication. Cryptocurrencies running on NeoScrypt are Feathercoin, GoByte, Desire and others.
- Keccak is an extension of SHA-256. Its middle name is SHA-3. The development was completed in 2013. Keccak cannot be called 100% resistant to ASICs, so device emergence is possible. Due to the peculiarities of the algorithm, it is not suitable for mining on a processor, so graphics cards are increasingly used for mining cryptocurrencies on Keccak.
- Quark is a secure and robust algorithm consisting of six parallel hashing processes. The feature makes the protocol resistant to hacking and attacks. Quark was created in 2013 by Aumasson, Meier, Naya-Plasencia and Henzen. The pros are combining PoS and PoW, keeping the ecosystem running smoothly, and protecting against system shutdowns. Cryptocurrencies: Quark, PIVX, Dimecoin.
The number of algorithms is much higher, but the options discussed are enough to start mining and choose a mining method.
Author bio

Jamie is a graduate MBA from the UCLA Anderson School of Management and now is engaged in cryptocurrency analytics and forecasts. She also writes extensively on the blockchain, cryptocurrency, and modern digital technologies for business.
Jamie’s Twitter: https://twitter.com/@JamieEMartinez1