Cloud Data Security: Complete Protection Guide
Most organizations now store critical business data in the cloud, and industry analysts consistently report that the vast majority of cloud security breaches stem from customer misconfiguration—not sophisticated hacking. As businesses migrate sensitive workloads to AWS, Azure, and Google Cloud, understanding cloud data security has shifted from “nice-to-have” to mission-critical.
This guide explains what cloud data security is, why it matters, how it works, and how to implement it effectively.
You’ll learn the core technologies, navigate the shared responsibility model, and discover a practical maturity framework to prioritize your security investments.
Who this is for: IT professionals, CISOs, security architects, and business decision-makers evaluating or managing cloud security programs.
Table of Contents
Cloud data security at a glance
- What is cloud data security? → Technologies, policies, and processes protecting sensitive data in cloud environments from breaches, loss, and unauthorized access.
- Why does it matter? → Prevents regulatory fines (GDPR, HIPAA), protects brand reputation, and reduces average breach costs (around $4.9M per incident).
- Biggest risk? → Misconfiguration drives the vast majority of cloud breaches—not external hacking.
- Who’s responsible? → Shared model: Cloud providers secure infrastructure; customers secure their data, apps, and access controls.
- How to start? → Assess your data estate, classify sensitivity levels, implement encryption and IAM, then monitor continuously.
What Is Cloud Data Security?

Cloud data security is the practice of protecting sensitive data stored, processed, and transmitted in cloud environments from unauthorized access, breaches, and loss. It combines technologies like encryption and identity management with policies and processes to ensure data confidentiality, integrity, and availability across public, private, and hybrid clouds.
Cloud data security addresses three critical data states:
- Data at-rest: Information stored in databases, object storage, or backups
- Data in-transit: Information moving between services, networks, or locations
- Data in-use: Information actively processed in memory or applications
Unlike traditional on-premise security that relies on physical perimeters and network boundaries, cloud data security operates in dynamic, distributed environments where resources scale automatically and data flows across multiple services, regions, and sometimes providers. This fundamental shift demands new security approaches tailored to cloud architecture.
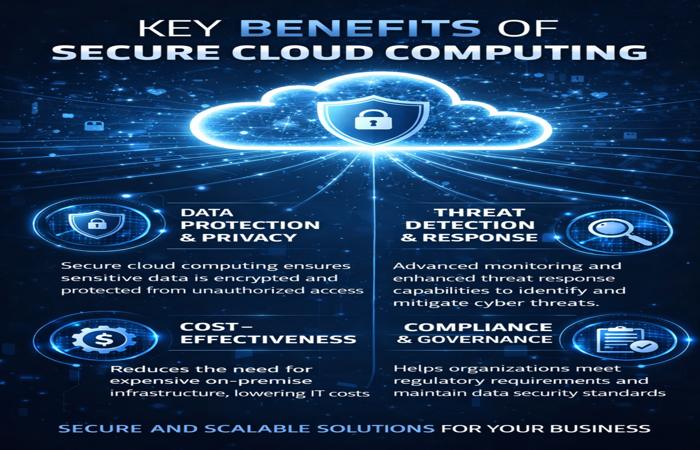
Why Cloud Data Security Matters
Regulatory Compliance (GDPR, HIPAA, SOC 2)
Organizations handling personal data, healthcare information, or financial records face strict legal obligations. The General Data Protection Regulation (GDPR) requires appropriate technical measures including encryption and pseudonymization, as defined by GDPR Article 32 on data protection. Violations carry fines up to €20 million or 4% of global revenue.
Healthcare organizations must comply with HIPAA requirements for protecting patient data. Financial services face PCI DSS mandates for payment information. Cloud data security controls provide the technical foundation for meeting these obligations.
Business Continuity and Disaster Recovery
Cloud data security includes backup strategies and disaster recovery planning that protect against data loss from hardware failures, natural disasters, or cyberattacks. Modern cloud platforms offer geographic redundancy and automated failover, but only when properly configured.
Organizations without robust cloud data security risk extended downtime during incidents. Recovery time objectives (RTO) and recovery point objectives (RPO) depend directly on security and backup architecture quality.
Brand Reputation and Customer Trust
Data breaches damage customer confidence and brand equity. High-profile incidents at major companies demonstrate how quickly trust erodes after security failures become public.
B2B customers increasingly require security certifications (SOC 2, ISO 27001) before signing contracts. Cloud data security directly enables these certifications and competitive differentiation.
Financial Impact of Data Breaches
The average data breach cost reached around $4.88 million in 2024, according to IBM’s Cost of a Data Breach Report, with costs continuing to rise. This includes incident response, legal fees, regulatory fines, customer notification, credit monitoring services, and lost business.
Cloud-specific breaches often carry higher costs due to complexity of multi-cloud investigations, potential exposure of customer data across regions, and regulatory notification requirements across multiple jurisdictions.
ROI justification: Security investments should be proportional to breach risk exposure. A simple calculation helps justify spend: if your annual breach probability is 10% and average breach cost is $4.88M, your expected annual loss is about $488K. Security investments under this threshold demonstrate positive ROI—before factoring in reputation damage, customer churn, or regulatory fines that multiply the total cost.
How Cloud Data Security Works
Core Principles (CIA Triad: Confidentiality, Integrity, Availability)
Cloud data security architecture rests on three fundamental principles:
Confidentiality: Ensuring only authorized users and systems can access sensitive data. Achieved through encryption, access controls, and authentication mechanisms.
Integrity: Guaranteeing data remains accurate and unaltered except through authorized changes. Protected by checksums, version control, and audit logging that detect unauthorized modifications.
Availability: Ensuring authorized users can access data when needed. Maintained through redundancy, failover systems, DDoS protection, and disaster recovery planning.
These principles guide every cloud data security decision, from choosing encryption methods to designing access policies.
The Shared Responsibility Model
Cloud security operates under a shared responsibility model where the cloud provider and customer each own specific security domains. According to AWS’s shared responsibility model framework, the provider secures the physical infrastructure, network, and virtualization layer (“security OF the cloud”), while customers secure their data, applications, and access controls (“security IN the cloud”).
The exact division depends on your service model:
| Security Area | IaaS (Infrastructure) | PaaS (Platform) | SaaS (Software) |
|---|---|---|---|
| Physical infrastructure | Provider | Provider | Provider |
| Network infrastructure | Provider | Provider | Provider |
| Virtualization layer | Provider | Provider | Provider |
| Operating system | Customer | Provider | Provider |
| Application | Customer | Customer | Provider |
| Data | Customer | Customer | Customer |
| Access management | Customer | Customer | Customer |
Critical insight: Regardless of service model, you always own responsibility for your data and who can access it. Cloud providers secure the platform; you secure what you put on it.
Key Cloud Data Security Technologies

Data Encryption (At-Rest, In-Transit, In-Use)
Encryption transforms readable data into ciphertext using cryptographic algorithms, rendering it useless without the decryption key. Modern cloud data security requires encryption across all three data states.
At-rest encryption protects stored data in databases, object storage (S3, Azure Blob), and backups using AES-256 symmetric encryption. Cloud providers offer:
- Provider-managed keys: Automated encryption with provider-controlled keys (easiest but less control)
- Customer-managed keys: You control key lifecycle through services like AWS KMS or Azure Key Vault (higher security, more management)
- Customer-provided keys: You generate and manage keys entirely outside the cloud (maximum control, maximum complexity)
In-transit encryption secures data moving between services or users using TLS 1.2+ protocols. This prevents interception during network transmission. Most cloud providers enforce TLS by default for API calls and service communication.
In-use encryption (also called confidential computing) protects data actively processed in memory. Technologies like Intel SGX or AMD SEV create isolated execution environments where even the cloud provider cannot access decrypted data. This emerging area addresses the final frontier of cloud data protection. For detailed guidance on selecting the right key management approach, consult your cloud provider’s encryption and key management documentation or established security frameworks such as NIST recommendations.
Identity and Access Management (IAM)
IAM systems control who can access which resources under what conditions. Cloud IAM operates through:
- Role-Based Access Control (RBAC): Assigns permissions to roles (e.g., “Database Administrator”) rather than individuals. Users inherit permissions by assuming roles. This simplifies management as team members change.
- Attribute-Based Access Control (ABAC): Grants access based on attributes like department, location, or data classification level. Provides more granular control than RBAC for complex organizations.
- Multi-Factor Authentication (MFA): Requires two or more verification methods (password + hardware token, biometric + SMS code). According to Microsoft security research on identity protection, MFA can block the vast majority of automated account compromise attacks.
- Principle of Least Privilege: Users receive only the minimum permissions needed for their role. This limits damage from compromised accounts or insider threats.
Organizations seeking maximum access control should explore Zero Trust architecture patterns described in official cloud provider documentation and trusted security frameworks (such as NIST and CISA guidance).
Data Loss Prevention (DLP)
DLP systems detect and prevent sensitive data from leaving your control. Cloud DLP tools scan data flows in real-time, identifying patterns like:
- Credit card numbers (PCI DSS patterns)
- Social Security numbers
- Healthcare records (PHI)
- Custom patterns you define (proprietary data formats)
When DLP detects sensitive data in unauthorized contexts (being uploaded to personal cloud storage, sent via unencrypted email), it can:
- Block the action entirely
- Alert security teams for investigation
- Encrypt automatically before allowing transfer
- Redact sensitive portions while allowing the rest
Modern cloud DLP integrates with cloud storage (S3, Google Cloud Storage), SaaS apps (Microsoft 365, Salesforce), and collaboration tools (Slack, Teams).
Cloud Security Posture Management (CSPM)
CSPM platforms continuously scan your cloud configurations, comparing them against security best practices and compliance benchmarks. They identify:
- Publicly exposed storage buckets
- Overly permissive IAM policies
- Missing encryption settings
- Unused credentials or orphaned resources
- Non-compliant configurations for GDPR, HIPAA, etc.
CSPM tools integrate with AWS, Azure, GCP, and multi-cloud environments through APIs, providing a unified security view across your entire cloud estate. They prioritize risks by severity and exploitability, helping teams focus on critical misconfigurations first.
Security Information and Event Management (SIEM)
SIEM solutions aggregate security logs from all cloud services into a central platform for analysis. They correlate events across systems to detect attack patterns like:
- Multiple failed login attempts (brute force attacks)
- Unusual data access patterns (potential data exfiltration)
- Privilege escalation attempts
- Suspicious API calls
Cloud-native SIEM tools (like AWS Security Lake, Azure Sentinel, Google Chronicle) integrate directly with cloud provider logs, reducing setup complexity and providing pre-built detection rules for common cloud threats.
Top Cloud Data Security Risks and Challenges
Misconfiguration (The #1 Cause of Breaches)
According to Gartner research on cloud security, misconfiguration is responsible for the vast majority of cloud security breaches, rather than sophisticated provider-side failures.
- Public S3 buckets exposing customer databases (Capital One breach, 2019)
- Disabled encryption on storage services
- Overly permissive IAM policies granting broad access
- Unpatched vulnerabilities in cloud-hosted applications
Why this happens: Cloud platforms offer thousands of configuration options. Default settings often prioritize ease-of-use over security. A single misconfigured setting can expose terabytes of sensitive data.
Prevention approach: Implement CSPM tools, use infrastructure-as-code templates with security baked in, and conduct regular configuration audits against CIS Benchmarks or cloud provider security baselines.
Insufficient Access Controls
Weak authentication or overly broad permissions create attack opportunities:
- Shared credentials: Multiple users using single admin accounts eliminate accountability
- Stale credentials: Former employees retaining access after departure
- Service account sprawl: Applications with excessive permissions
The 2020 SolarWinds attack demonstrated how compromised credentials with broad cloud access enabled attackers to pivot across customer environments for months undetected.
Insider Threats and Account Hijacking
Authorized users with malicious intent or compromised accounts pose significant risks:
- Malicious insiders can exfiltrate data gradually to avoid detection
- Phishing attacks trick employees into revealing credentials
- Social engineering manipulates users into granting access or downloading malware
According to Verizon’s Data Breach Investigations Report, insider threats account for approximately 20% of breaches, with privileged user abuse being particularly damaging.
API Vulnerabilities
Cloud services rely heavily on APIs for functionality. Unsecured APIs create attack surfaces through:
- Broken authentication: APIs lacking proper token validation
- Excessive data exposure: APIs returning more data than necessary
- Lack of rate limiting: Enabling brute-force or denial-of-service attacks
- Insufficient logging: Making breach detection difficult
The Facebook data leak affecting 533 million users (2021) originated from an API vulnerability allowing mass data scraping.
Shadow IT and Unsanctioned Apps
Employees adopting cloud services without IT approval create security blind spots:
- Unknown SaaS applications processing company data
- Personal cloud storage used for business files
- Unsanctioned collaboration tools lacking security controls
Shadow IT circumvents security policies, compliance controls, and monitoring systems. IT departments cannot protect data in systems they don’t know exist.
Multi-Cloud Complexity
While 85% of enterprises now use multi-cloud strategies, security complexity grows exponentially—not linearly. Challenges include:
- Inconsistent security policies across AWS, Azure, and GCP
- Fragmented visibility: Each provider offers different monitoring tools
- Cross-cloud data flows: Difficult to track and secure data moving between clouds
- Alert fatigue: Multiple security dashboards generating duplicate or conflicting alerts
Each additional cloud platform introduces new configuration requirements, IAM models, and security tooling, multiplying the potential for misconfiguration and gaps. Organizations managing multiple cloud platforms should consider unified security approaches and tools specifically designed for securing multi-cloud environments.
Cloud Data Security Best Practices
Baseline Security (Must-Have)
1. Conduct comprehensive data discovery and classification
You cannot protect data you don’t know exists. Begin with complete visibility into your cloud data estate:
- Inventory all cloud storage locations (databases, object storage, file shares)
- Identify sensitive data types (PII, financial, healthcare, intellectual property)
- Classify data by sensitivity level (Public / Internal / Confidential / Restricted)
- Map data flows between services and across cloud boundaries
Use automated discovery tools rather than manual audits. Cloud environments change constantly—today’s inventory becomes outdated within days.
2. Enable encryption for data at-rest and in-transit
Almost all compliance frameworks mandate encryption. Implement:
- At-rest: Enable AES-256 encryption for all storage services (databases, S3/Blob storage, backups)
- In-transit: Enforce TLS 1.2+ for all network communication; disable older protocols (SSL, TLS 1.0/1.1)
- Key management: Start with customer-managed keys through cloud provider KMS for control without excessive complexity
Encryption makes stolen data unusable to attackers. Even if a misconfigured bucket is exposed, encrypted data remains protected (assuming keys are properly secured).
3. Implement strong identity and access management
Access control failures enable most cloud breaches:
- Enforce MFA on all user accounts, especially privileged/admin accounts
- Apply least privilege: Grant minimum permissions necessary for each role
- Use role-based access control (RBAC): Assign permissions to roles, not individuals
- Eliminate shared credentials: Every user and service needs unique identities
- Rotate credentials regularly: Passwords every 90 days; API keys and service credentials every 30-90 days
Configure automated alerts for suspicious authentication patterns: logins from unusual locations, multiple failed attempts, or privilege escalation actions.
4. Establish continuous monitoring and logging
Cloud environments change rapidly. Real-time monitoring detects threats before they escalate:
- Enable comprehensive logging: Capture authentication, API calls, configuration changes, and data access
- Centralize logs: Use SIEM solutions to aggregate logs from all cloud services
- Set up alerting: Trigger notifications for critical events (admin changes, bulk data downloads, failed access attempts)
- Retain logs appropriately: Typically 90 days minimum; 1+ years for compliance requirements
Monitoring provides the visibility needed for incident detection and forensic investigation after breaches.
Enhanced Security (Recommended)
5. Deploy Data Loss Prevention (DLP) solutions
DLP prevents sensitive data from leaving your control:
- Configure DLP policies to detect PII, financial data, healthcare records, or custom patterns
- Block or encrypt sensitive data shared through unsanctioned channels
- Monitor cloud storage for sensitive data in wrong locations or with wrong permissions
- Integrate DLP with email, collaboration tools (Slack, Teams), and cloud storage
Cloud-native DLP services (like Google Cloud DLP or Microsoft Purview) integrate seamlessly with cloud platforms and require minimal infrastructure.
6. Implement Cloud Security Posture Management (CSPM)
CSPM tools continuously assess cloud configurations against security benchmarks:
- Scan for misconfigured storage buckets, databases, and network settings
- Identify overly permissive IAM policies or inactive credentials
- Validate encryption is enabled across all required services
- Check compliance against frameworks (CIS Benchmarks, NIST, PCI DSS)
CSPM provides automated remediation suggestions and tracks risk reduction over time. Leading solutions include Wiz, Prisma Cloud, and native cloud provider tools (AWS Security Hub, Azure Security Center).
7. Secure APIs and service integrations
APIs connect cloud services but create attack surfaces when improperly secured:
- Authenticate all API requests: Use OAuth 2.0, API keys with strict rotation, or JWT tokens
- Implement rate limiting: Prevent brute-force attacks and resource abuse
- Validate input rigorously: Protect against injection attacks
- Minimize data exposure: APIs should return only necessary information
- Log all API activity: Track usage patterns to detect anomalies
Regular API security testing and penetration testing identify vulnerabilities before attackers exploit them.
8. Address shadow IT with visibility tools
Combat unsanctioned cloud service adoption:
- Deploy Cloud Access Security Brokers (CASB) to discover all cloud applications in use
- Analyze network traffic to identify unauthorized SaaS connections
- Create approved cloud service catalogs with pre-vetted security
- Educate employees on risks of using personal cloud accounts for business data
Rather than simply blocking shadow IT, provide secure approved alternatives that meet employee needs while maintaining security control.
Advanced Security (Enterprise-Grade)
9. Adopt Zero Trust architecture
Zero Trust operates on “never trust, always verify”:
- Verify explicitly: Authenticate and authorize every access request using all available data (identity, location, device health, data sensitivity)
- Use least privilege access: Grant just-in-time, just-enough-access; limit user and service permissions
- Assume breach: Design security assuming attackers are already inside; segment networks and applications to contain damage
Zero Trust eliminates implicit trust based on network location, treating all users and devices as potentially compromised until proven otherwise.
10. Implement automated backup and disaster recovery
Ransomware and data corruption make backups essential:
- Follow the 3-2-1-1-0 rule: Three copies of data, on two different media types, with one copy offsite, one offline (air-gapped), and zero errors verified
- Automate backup processes: Eliminate reliance on manual procedures
- Test recovery regularly: Quarterly restore drills ensure backups actually work
- Separate backup credentials: Use different authentication than production systems to prevent attackers from encrypting backups
Cloud-native backup services (AWS Backup, Azure Backup) integrate with cloud resources but require proper configuration to provide meaningful protection.
11. Establish incident response procedures
Preparation reduces breach impact and recovery time:
- Create a detailed response playbook for common cloud attack scenarios (ransomware, data exfiltration, account compromise)
- Define roles and responsibilities: Who investigates? Who communicates with customers? Who handles legal/regulatory reporting?
- Maintain updated contact lists for internal stakeholders and external parties (forensics firms, legal counsel, cyber insurance)
- Conduct tabletop exercises simulating breach scenarios to test response effectiveness
Document your incident response plan and review it quarterly as cloud architecture evolves.
Quick-Win Security Checklist
You can implement these actions this week:
- Enable MFA on all admin/privileged accounts
- Review and remove inactive user accounts
- Enable encryption on all S3 buckets / Blob storage
- Audit IAM policies for overly permissive access
- Enable CloudTrail / Activity Logs for all accounts
- Review publicly accessible resources (use AWS Access Analyzer or similar)
Cloud Data Security Maturity Model
Organizations should scale security investments proportionally to data sensitivity and compliance requirements. This framework helps prioritize implementation:
| Maturity Tier | Security Controls | Best For | Implementation Effort | Self-Assessment Criteria |
|---|---|---|---|---|
| Baseline | • Provider-managed encryption• MFA on admin accounts• Basic IAM with RBAC• Native cloud monitoring• Weekly configuration reviews | • Startups and SMBs• Non-regulated industries• Low-to-medium sensitivity data | Low (2-4 weeks) | ☑ No encryption enabled OR using only defaults☑ Some accounts lack MFA☑ No formal monitoring process |
| Enhanced | All Baseline controls, plus:• Customer-managed encryption keys• DLP policies• CSPM scanning• SIEM integration• Automated compliance monitoring | • Mid-size enterprises• Regulated industries• Multi-cloud environments• High-sensitivity data | Medium (2-3 months) | ☑ Encryption enabled but provider-managed☑ MFA on admin accounts only☑ Basic CSPM or manual audits☑ No DLP or limited coverage |
| Maximum | All Enhanced controls, plus:• Zero Trust architecture• In-use encryption (confidential computing)• Advanced threat detection (UEBA)• 24/7 SOC monitoring• Regular penetration testing | • Large enterprises• Healthcare and finance• Government contractors• Critical infrastructure | High (4-6 months+) | ☑ Customer-managed encryption keys☑ MFA enforced universally☑ Zero Trust implemented☑ 24/7 monitoring with SOC☑ Regular penetration testing |
How to use this framework: Start at Baseline, measure your risk exposure and compliance needs, then advance to Enhanced or Maximum as your cloud maturity and budget allow. Avoid jumping directly to Maximum security unless regulatory requirements demand it—complexity itself creates security risks through difficult-to-manage configurations.
Cloud Data Security Implementation Roadmap
Phase 1: Assess and Discover (30-60 days)
Goal: Understand what data you have and where it lives.
Key activities:
- Inventory all cloud accounts, subscriptions, and projects across providers
- Discover all data repositories (databases, storage buckets, file shares, SaaS applications)
- Identify sensitive data using automated scanning tools
- Document current security controls and configurations
- Map data flows between services and systems
Deliverables: Complete data inventory, sensitivity classification, current security posture baseline.
Phase 2: Classify and Prioritize (30-45 days)
Goal: Determine protection requirements for each data asset.
Key activities:
- Apply classification labels (Public / Internal / Confidential / Restricted)
- Assess risk for each data type (likelihood of breach × potential impact)
- Identify compliance requirements (GDPR, HIPAA, PCI DSS, SOC 2)
- Prioritize security investments based on risk scores
- Define acceptable risk thresholds for non-critical data
Deliverables: Data classification taxonomy, risk assessment report, prioritized security roadmap.
Phase 3: Implement Core Controls (60-90 days)
Goal: Deploy essential security technologies and policies.
Key activities:
- Enable encryption (at-rest and in-transit) on all services
- Implement IAM with least privilege and MFA
- Deploy CSPM for continuous configuration monitoring
- Establish baseline logging and monitoring
- Configure automated alerting for critical events
- Document security policies and procedures
Deliverables: Encrypted storage, enforced access controls, active monitoring, documented security policies.
Phase 4: Monitor and Optimize (Ongoing)
Goal: Maintain security posture as environment evolves.
Key activities:
- Review CSPM findings weekly; remediate high/critical issues within 48 hours
- Conduct quarterly access reviews (remove stale accounts and permissions)
- Test disaster recovery procedures quarterly
- Update security policies as new services are adopted
- Track security metrics (time-to-detect, time-to-remediate, misconfiguration trends)
- Provide ongoing security awareness training
Deliverables: Continuously improved security posture, compliance maintenance, reduced attack surface over time.
Common Mistakes and Pitfalls to Avoid
1. Trusting default cloud configurations
Cloud providers default to usability, not maximum security. Many breaches occur because teams assume default settings are secure. Always harden configurations using provider security benchmarks.
2. Neglecting the shared responsibility model
Assuming “the cloud provider handles security” leaves critical gaps. As explained in the shared responsibility model, you always own responsibility for your data, access controls, and application security regardless of service model.
3. Implementing all-or-nothing security approaches
Attempting enterprise-grade security from day one often fails due to complexity and cost. Start with baseline controls, then mature incrementally based on risk and compliance needs.
4. Ignoring existing security tools and processes
Cloud security should extend your existing security program, not replace it entirely. Integrate cloud monitoring into existing SIEM rather than creating parallel security operations.
5. Overlooking data residency and sovereignty requirements
Global operations face regulations that may require certain types of personal data to stay within specific geographic regions. Many organizations choose to keep EU personal data in EU regions to simplify GDPR compliance and data transfer obligations, while China’s data laws often require local storage. Plan cloud regions carefully to maintain compliance.
6. Failing to test disaster recovery
Untested backups frequently fail when needed. Organizations discover during ransomware incidents that backup configurations were incomplete or restoration procedures don’t work. Test recovery quarterly at minimum.
Who This Is For / Who Should Proceed with Caution
Best For:
- Cloud-native organizations storing sensitive customer data, financial information, or intellectual property
- Enterprises subject to regulatory compliance (GDPR, HIPAA, PCI DSS, SOC 2)
- Companies using multi-cloud or hybrid environments requiring unified security policies
- IT teams with moderate-to-advanced cloud expertise capable of implementing and managing security controls
Proceed with Caution:
- Organizations with zero cloud experience: Consider managed security services or cloud migration partners rather than DIY security implementation
- Very small teams (1-2 IT staff) without dedicated security personnel: Start with provider-managed security defaults and scale as team grows
- Ultra-low-budget startups: Prioritize encryption and IAM (low-cost essentials), defer advanced tools (CSPM, DLP) until funding allows
Not Recommended For:
- Fully on-premise operations with no cloud migration plans: Focus on traditional network security instead
- Organizations handling extremely high-risk data (classified government information, critical infrastructure) without qualified security teams: Requires specialized expertise beyond general cloud data security
Final Verdict
Cloud data security is non-negotiable for organizations storing sensitive data in AWS, Azure, Google Cloud, or SaaS applications. The shared responsibility model places data protection, access control, and configuration management squarely in your hands—cloud providers secure the platform, but you secure what you put on it.
The single most important action: Address misconfiguration through CSPM tools and regular audits. This significantly reduces the likelihood of cloud breaches and costs far less than responding to incidents.
Start with the Baseline security tier (encryption, IAM, MFA, monitoring), then advance based on your risk profile and compliance requirements. Attempting maximum security without phased implementation typically results in complexity that creates new vulnerabilities.
Recommended next steps:
- Conduct a cloud data inventory to understand what you’re protecting
- Enable MFA and encryption across all cloud accounts this week
- Deploy a CSPM tool to identify your top 10 misconfigurations
- Create an incident response plan before you need one
- Review a cloud security compliance checklist aligned with your industry standards (such as GDPR, HIPAA, PCI DSS, or SOC 2) to ensure you meet baseline requirements.
Cloud data security is a continuous journey, not a one-time project. Build incrementally, measure continuously, and adjust as your cloud environment evolves.
Frequently Asked Questions
Q: What is cloud data security?
A: Cloud data security is the practice of protecting sensitive data in cloud environments from unauthorized access, breaches, and loss through technologies like encryption and IAM, combined with security policies and processes. It ensures data confidentiality, integrity, and availability across public, private, and hybrid clouds.
Q: How is data protected in the cloud?
A: Data protection in the cloud uses multiple layers: encryption (making data unreadable without keys), identity and access management (controlling who can access what), data loss prevention (blocking unauthorized transfers), continuous monitoring (detecting suspicious activity), and automated backups (enabling recovery). These controls work together to create defense-in-depth.
Q: What are the biggest risks to cloud data security?
A: The top risks are misconfiguration (driving the vast majority of breaches), insufficient access controls (weak passwords, excessive permissions), insider threats (malicious or negligent employees), API vulnerabilities (unsecured service connections), and shadow IT (unsanctioned cloud services). Misconfiguration is by far the most common cause of data exposure.
Q: Who is responsible for cloud data security?
A: Cloud security follows a shared responsibility model. Cloud providers (AWS, Azure, GCP) secure the physical infrastructure, network, and virtualization layer. Customers secure their data, applications, access controls, and configurations. Regardless of service model, customers always own responsibility for their data and who can access it.
Q: Is cloud storage more secure than on-premise?
A: Cloud storage can be more secure when properly configured. Major providers invest heavily in physical security, network protection, and threat detection at scale most organizations cannot match. However, cloud security depends entirely on correct configuration—default settings are often insecure. Well-managed on-premise systems can be more secure than poorly configured cloud environments.
Q: What is the difference between CSPM and DSPM?
A: CSPM (Cloud Security Posture Management) monitors cloud configurations (storage permissions, network settings, IAM policies) to identify misconfigurations. DSPM (Data Security Posture Management) focuses specifically on data risks—where sensitive data is stored, who can access it, and whether it’s properly protected. DSPM is data-centric; CSPM is infrastructure-centric.